Enterprise Zero Trust Architecture: Implementation Guide & Business Benefits (Updated 2026)

Most enterprises don’t have a cybersecurity problem. They have a trust problem.
Firewalls are in place. Tools are deployed. Compliance boxes are checked. And still, breaches happen. Not because your security team is missing something—but because the “inside equals safe” model is a relic that doesn’t survive 2026.
Here is the uncomfortable truth: In the USA, the average cost of a data breach has hit $10.8M. When you factor in the global cybercrime damage projections, which are hitting record highs in 2026, it’s clear this isn’t just a technical glitch. For a Fortune 1000, a breach isn’t an “IT incident”; it’s a direct hit to the quarterly EPS.
Organizations with mature Zero Trust architectures aren’t just “safer”—they save $1.85M per incident by containing the fire before it guts the entire building.
But let’s be real: Zero Trust is hard. It’s not a software you buy; it’s a capital allocation decision that usually dies in the boardroom due to “people politics” and legacy debt. This guide skips the theory and looks at how to actually implement Zero Trust without breaking your production environment.
What Is Enterprise Zero Trust Architecture?
Stop thinking of Zero Trust as a “product” you install. It’s a culture of systematic skepticism.
In a traditional network, once you’re in, you’re “trusted.” In an Enterprise Zero Trust model, we assume the bad guy is already sitting in your HR manager’s laptop. Every single move—from opening a PDF to accessing a database—requires a “digital ID check.”
The 3 Pillars (Without the Fluff):
- Identity is the New Perimeter: It doesn’t matter if you’re calling from the office or a Starbucks in Dubai. If your device posture (updates, encryption) isn’t perfect, you don’t get in.
- Microsegmentation (The Fire Doors): Think of a submarine. If one compartment floods, you seal the door so the whole ship doesn’t sink. In 2026, if a ransomware hits your marketing folder, it shouldn’t be able to “jump” to your financial servers.
- The “Least Privilege” Rule: If an intern only needs access to Canva, they shouldn’t even see the link to the payroll system.
The Reality Check: > Why does this matter? Because the average breach lives in your system for 241 days before you notice (IBM 2026). Zero Trust cuts that time in half.
But here is what your software vendor won’t tell you: Implementing this is an operational nightmare at first. Employees hate extra login steps, and if you segment your network too aggressively without mapping dependencies, you’ll break your own company. It’s a balance of security vs. “getting work done.”

Why Traditional Perimeter Security Fails
Traditional security is built on a lie: that everyone inside your office walls is “good.”
In the real world, 22% of breaches start with a simple stolen password (Verizon 2025). Your $50,000 firewall doesn’t care if a hacker uses a valid admin password—it just lets them in. Once they are inside, they have “the keys to the kingdom.”
The $1 Million-an-Hour Nightmare
For a large enterprise, downtime isn’t just an annoyance; it’s a $1 million-per-hour drain on revenue (Cybersecurity Ventures 2025). Cloud attacks didn’t just grow; they exploded by 75% last year. If you are still relying on a “digital moat,” you aren’t securing your data—you’re just waiting for the bill.
Case in Point: The 17-Application Domino Effect
I saw this happen with a global logistics firm. One admin account—just one—was compromised via a simple phishing link. Because they had no internal “fire doors” (Zero Trust), the attacker jumped through 17 different applications in four hours. By the time the IT team finished their morning coffee, the financial systems were already being encrypted.
Why do companies still fail here?
Because changing the perimeter is painful. It requires audits, killing old “legacy” apps that everyone loves, and admitting that your current security is theater. Most firms wait for a breach to happen before they find the budget to fix it.
Strategic & Financial Comparison: The Cost of “Trust”
| The Business Pain | Traditional (The Risk) | Zero Trust (2026) | The Money Talk |
| Who gets in? | Anyone with a password | Only verified “postures” | 50% faster detection |
| Internal Access | “Wild West” (Open) | Submarine-style doors | -80% attack spread |
| Cloud Safety | Porous / Weak | Identity-centric | Saves $5.2M per breach |
| Insurance | High Premiums | Baseline Requirement | Avoids 3x price hikes |
| The SEC Audit | “We tried our best” | Native Compliance | Zero regulatory fines |

The Bottom Line: Traditional security tries to stop the break-in. Zero Trust assumes the burglar is already in the kitchen and locks the door to the safe. In 2026, if you aren’t using an identity-centric model, you aren’t just an IT laggard—you’re a material risk to your shareholders.
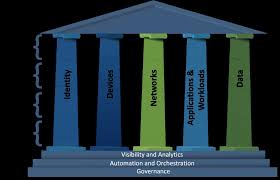
Zero Trust Architecture Framework: Core Components
Implementing Zero Trust isn’t about buying a “bundle” of tools. It’s about orchestrating specific components that actually talk to each other. If they don’t, you just have a very expensive collection of dashboards.
According to NIST SP 800-207, these are the pillars, but here is the “battle-scarred” take on what actually matters in 2026:
- Identity as the New Perimeter (IAM): In a world of remote work and APIs, your office walls don’t exist. Your “perimeter” is now a set of login credentials and device fingerprints. Warning: If your IAM is messy, your Zero Trust is a house of cards.
- Adaptive MFA (Not just SMS): If you are still using SMS codes, you are failing. High-maturity enterprises are moving toward FIDO2 passwordless authentication standards or biometric pushes. It stops 99% of bulk credential attacks before they even hit your server.
- Microsegmentation (The Heavy Lifter): This is the hardest part to get right. By isolating workloads, you reduce lateral movement by 80% (Gartner 2025). Real-world tip: Don’t try to segment everything at once. Start with your “crown jewels”—the databases that would end your company if leaked.
- Endpoint Hygiene: You can’t trust a user if their laptop is running an unpatched OS from 2022. Identity is half the battle; the health of the device is the other half.
- Continuous Monitoring & SOAR: Humans can’t watch logs 24/7. You need AI-assisted analytics to spot a login from London and a file download from Tokyo happening at the same time.
The “Least Privilege” Reality Check: Most breaches happen because someone has “God Mode” access when they only need to read a spreadsheet. Zero Trust enforces “Just-in-Time” access: you get the keys when you need them, and they expire when you’re done.
How to Implement Enterprise Zero Trust Architecture in a Large Organization
Implementation is where most “Strategy ppts” go to die. You can’t just flip a switch and be “Zero Trust.” It’s a multi-year grind of cleaning up decade-old technical debt.
Here is the realistic roadmap for a large-scale rollout in 2026:
- Phase 1: The “Crown Jewel” Audit: Forget mapping everything. You don’t have the time. Identify the 3-5 databases that, if leaked, would put your CEO in front of a Senate committee. Map those identity flows first. If you don’t know where the money is, you can’t protect it.
- Phase 2: The Identity Cleanup: Before you buy fancy tools, fix your Active Directory. Most breaches happen because an ex-employee’s account from 2019 still has “admin” rights. This phase is boring, manual, and absolutely non-negotiable.
- Phase 3: Tactical Microsegmentation (The Danger Zone): This is where you build the “fire doors.” Warning: If you segment too fast without understanding app dependencies, you will break your production environment. Start with “monitoring mode”—see what talks to what before you start cutting off connections.
- Phase 4: Taming the Legacy Beast: You will have 20-year-old apps that don’t support modern MFA. Don’t try to “fix” them; wrap them in a Zero Trust proxy. It’s about putting a modern vault around an old wooden box.
- Phase 5: AI-Assisted Tuning: Once the plumbing is done, let the machines watch the logs. AI-assisted detection isn’t just a buzzword; it saves $1.9M per incident (IBM 2026) by spotting a breach in minutes instead of months.
The Hard Truth on ROI: Treat this as a risk mitigation program, not a “project” with an end date. If your CFO asks for a 6-month completion date, tell them the truth: You are never “done” with Zero Trust. You are just consistently less vulnerable than your competitors.
The Zero Trust Maturity Model: Where Do You Actually Stand?
Most companies claim they are “doing Zero Trust” because they turned on MFA for their email. That is a dangerous delusion. Zero Trust is a spectrum of maturity, not a binary “yes” or “no.”
Here is the 2026 reality of where your budget sits vs. your actual risk:
- Level 1 — The Sitting Duck (Basic): You have MFA on some apps, but your internal network is a “Wild West.” If a hacker gets one password, they own the whole company.
- Financial Reality: You are staring at the full $10.8M average breach cost. Your insurance will likely deny your claim for “negligence.”
- Level 2 — The Identity Gatekeeper: You’ve centralized your IAM (Identity and Access Management). You know who is logging in, but once they are in, you stop watching. It’s better, but lateral movement is still easy.
- Level 3 — The Submarine (Segmented): This is the sweet spot for many mid-sized enterprises. You have Microsegmentation. If the marketing department gets hit, the financial servers stay locked. You’ve built “fire doors” that actually work.
- Level 4 — The AI-Assisted Fortress: You aren’t just locking doors; you are watching behavior. If an admin logs in at 3:00 AM from a new device to download 40GB of data, the system kills the session automatically.
- The Payoff: You detect breaches 80 days faster and save an average of $1.9M per incident (IBM 2026).
- Level 5 — Full Orchestration: This is the gold standard. Every API, every bot, and every employee is verified every second. At this level, your cybersecurity isn’t a cost—it’s a competitive advantage that lowers your insurance premiums by up to 40%.
2026 Reality Check: AI & The Legacy Beast
If you think protecting your employees is enough, you are ignoring 95% of your attack surface. In 2026, security is no longer just a “people problem.”
The 45:1 Ratio: Your Biggest Blind Spot For every human employee in your company, you now have an average of 45 non-human identities (APIs, AI agents, service accounts) accessing your sensitive data. Most of these “machine identities” don’t have MFA, they never change passwords, and nobody is watching them. In a mature Zero Trust model, these bots must be treated with the same skepticism as a new intern with a master key.
Shadow AI: The New Data Leak The biggest risk today isn’t a shadowy hacker; it’s a marketing lead uploading your entire customer database to an external AI to “summarize the trends.” If your Zero Trust policies don’t cover data flows into third-party AI models, you aren’t secured—you are leaking proprietary intel in real-time.
The Insurance Trap Cyber insurers have stopped asking “if” you have security. They now demand to see your Zero Trust architecture. If you cannot prove microsegmentation and 100% MFA across all assets:
- Your premiums will spike by up to 300%.
- Or worse: You will be denied coverage entirely after a ransomware hit.
Taming the Legacy Beast You cannot put a silk suit on a pig. You will have 20-year-old applications that simply cannot support modern Zero Trust. Don’t waste millions trying to “update” them; isolate them. Wrap them in a modern access proxy and let them run in a digital cage where they can’t infect the rest of your network.
The 60-Second Boardroom Test: Are You Actually Ready?
Most executives think they are protected because they have a “Security Department.” This test is designed to strip away that comfort. Be honest—your shareholders and your cyber insurer certainly will be.
Score Each Question (Yes = 1 | No = 0)
- Identity Audit: Are 100% of your privileged accounts (admins, devs, executives) audited and rotated every 90 days?
- The Red Team Test: Have you simulated a lateral movement attack in the last 6 months to see how fast a hacker can reach your financial core?
- The Bot Problem: Are your non-human identities (APIs, bots, AI agents) monitored with the same rigor as your human employees?
- Dwell Time: Is your average breach detection time currently below 120 days? (The industry average is 241).
- Hard MFA: Do you enforce hardware keys or biometric MFA for 100% of your privileged access? (SMS does not count).
- Microsegmentation: Can you prove that a ransomware infection in Marketing cannot “jump” to your Production or HR servers?
- Insurance Baseline: Does your current cyber insurance policy explicitly require Zero Trust controls to maintain your coverage?
- NIST Alignment: Is your architecture officially aligned with NIST SP 800-207 for 2026 compliance?
Score Interpretation:
6–8 → Mature Zero Trust Posture: You have successfully shifted from “perimeter defense” to “identity centric.” You are likely seeing lower insurance premiums and a significantly faster incident response time.
0–2 → Critical Material Risk: You are essentially a “sitting duck.” A breach is not a possibility; it’s an appointment. Your exposure likely exceeds the $10.8M average.
3–5 → False Sense of Security: You have the tools, but not the architecture. You can stop a script kiddie, but a professional ransomware group will move laterally through your network in hours.

Zero Trust: FAQS
1. Will Zero Trust make my employees hate the IT department? Initially, yes. Adding MFA and verifying device posture adds friction. But in 2026, the alternative is a week of total company downtime during a ransomware recovery. The trade-off is simple: 5 seconds of friction today vs. 500 hours of paralysis tomorrow.
2. Can I achieve Zero Trust without replacing all my legacy hardware? Yes. You don’t need to rip and replace everything. You use Identity Proxies and Segmentation Gateways to “wrap” your old systems. It’s about building a modern vault around an old wooden box.
3. Is Zero Trust just a way for vendors to sell more subscriptions? Some try to treat it that way. But Zero Trust is a strategy, not a product. If a vendor tells you their “box” will give you 100% Zero Trust by next Friday, they are lying. It’s an architectural shift, not a software license.
4. How does this affect my Cyber Insurance premiums? In 2026, it’s the difference between having coverage and being “uninsurable.” If you can’t prove microsegmentation, expect your premiums to spike by 300% or your policy to be canceled entirely.
The Bottom Line: Cybersecurity as a Capital Allocation Decision
Enterprise Zero Trust is no longer a “tech trend.” It is a fiduciary responsibility.
With the average US breach cost hitting $10.8M and SEC disclosure rules tightening, you cannot afford to “trust” your internal network. Organizations that treat Zero Trust as a multi-year risk mitigation program aren’t just safer—they are more efficient, more insurable, and more resilient.
Key 2026 Takeaways for the Boardroom:
- The Identity Ratio: You are managing a 45:1 ratio of bots to humans. Protect the machines.
- The Financial Guardrail: AI-assisted detection saves $1.9M per incident. It’s an investment, not a cost.
- The Inevitability: Stop trying to stop the break-in. Focus on containing the fire.
In 2026, you aren’t just securing data; you are securing your stock price.

