Enterprise Cybersecurity Strategy: Risk Management and Business Resilience

Enterprise Cybersecurity Strategy is no longer just a technical back-office function; in today’s digital economy, it has become a board-level discipline that directly impacts revenue continuity, regulatory exposure, insurance eligibility, and long-term enterprise valuation.
Modern organizations operate across hybrid cloud environments, third-party SaaS ecosystems, remote work infrastructures, and globally distributed supply chains — learn how Cybersecurity Strategy for Small and Medium Businesses adapts these principles for SMBs. Each integration expands the attack surface and increases systemic risk.
Research from IBM Security consistently shows that enterprise data breaches remain among the most expensive operational risks businesses face. Annual investigations by Verizon also highlight credential abuse and ransomware as dominant entry vectors.
For executive leadership, cybersecurity now directly influences:
- Revenue continuity and operational uptime
- Regulatory compliance and audit outcomes
- Client contract qualification (especially enterprise procurement)
- Cyber insurance underwriting and premiums
- Investor and board confidence
Cybersecurity has evolved from infrastructure protection into structured enterprise risk governance, aligning technical controls with business objectives and measurable risk management.
What is Enterprise Cybersecurity ?
Enterprise cybersecurity is a governance-driven strategy that protects business systems, cloud environments, and sensitive data through structured risk management, security frameworks, identity controls, and continuous monitoring. It reduces financial impact, improves regulatory alignment, and strengthens operational resilience.
Quick Info Table
| Topic | Enterprise Cybersecurity Strategy |
|---|---|
| Updated | 2026 |
| Difficulty | Intermediate–Advanced |
| Reading Time | 18 minutes |
| Target Audience | CIOs, CISOs, IT Directors, Risk & Compliance Leaders |
What Is an Enterprise Cybersecurity Strategy?
Enterprise cybersecurity is the structured alignment of technical security controls with business risk tolerance, regulatory obligations, and operational priorities — a foundation of any effective Enterprise Cybersecurity Strategy. For deeper compliance guidance, see Cybersecurity Compliance Explained: SOC2, ISO27001 & GDPR.
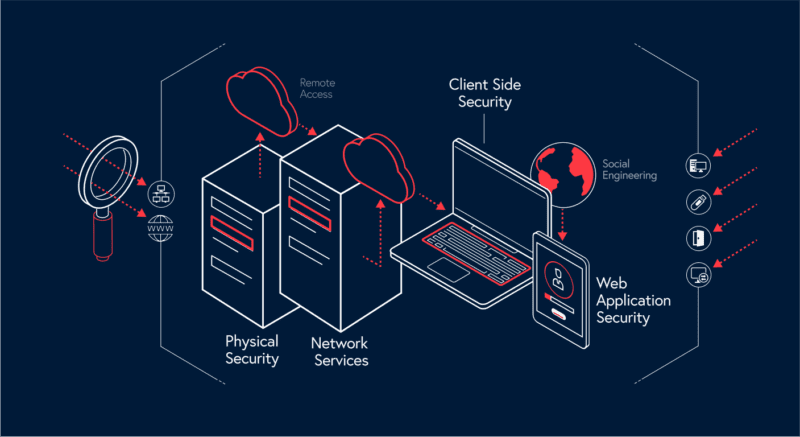
Unlike small business security models, enterprise environments assume:
- Continuous threat attempts
- Persistent adversaries
- Complex lateral movement risk
- Multi-layer vendor dependencies
A mature enterprise cybersecurity strategy typically integrates:
- Formal cybersecurity risk assessments
- Documented governance policies
- Identity and access management (IAM) programs
- Cloud and network architecture hardening
- Centralized monitoring and detection
- Structured incident response planning
The defining characteristic is integration. Security decisions intersect with finance, legal, procurement, and executive oversight. When cybersecurity becomes embedded into enterprise strategy rather than isolated within IT, resilience increases measurably.
Strategic Comparison: Traditional IT Security vs Enterprise Cybersecurity
| Dimension | Traditional IT Security | Enterprise Cybersecurity Strategy |
|---|---|---|
| Focus | Technical protection | Business risk governance |
| Reporting | IT department | Executive & board visibility |
| Metrics | Tool performance | Risk exposure & financial impact |
| Architecture | Perimeter-based | Identity-centric & Zero Trust |
| Incident Handling | Reactive | Structured response lifecycle |
| Vendor Risk | Limited | Integrated third-party oversight |
This distinction explains why many organizations believe they are “secure” while remaining strategically exposed. Enterprise cybersecurity aligns protection mechanisms with measurable business impact.

Discover the top Cybersecurity Threats Facing Businesses in 2026 to prioritize your defenses.
Cybersecurity as Business Risk Management
One of the most common weaknesses in growing organizations is treating cybersecurity as a technical cost center rather than a financial risk domain — instead of embedding it within a formal Enterprise Cybersecurity Strategy.
At enterprise scale, digital risk must be quantified in business terms, aligning with enterprise risk management frameworks and measurable cybersecurity KPIs:
- What is the cost per hour of downtime?
- What regulatory penalties apply to data exposure?
- What contractual obligations require specific security controls?
- What supply chain dependencies create cascading impact?
According to the IBM Cost of a Data Breach Report 2025, the average total cost of an enterprise data breach is $4.45 million, including detection, remediation, and business disruption costs. Meanwhile, research from Accenture shows that nearly 68% of business leaders indicate cyber risk as a top concern affecting investment decisions and operational planning.
When security teams translate cyber risk into financial and operational metrics, board engagement improves significantly.
Executive Insight
Boards rarely ask, “Are we secure?”
They ask, “What is our exposure, and how quickly can we contain disruption?”
Organizations that align cybersecurity reporting with enterprise risk management frameworks gain faster budget approvals and stronger executive alignment.
At this stage, enterprises often begin evaluating advanced cybersecurity risk assessment platforms that provide quantifiable exposure modeling rather than static compliance checklists.
Key Metrics That Reflect Enterprise Maturity
Advanced enterprises rely on measurable indicators rather than assumptions.
Critical cybersecurity KPIs include:
- Mean Time to Detect (MTTD)
- Mean Time to Respond (MTTR)
- Patch compliance percentages
- Privileged access review frequency
- Endpoint and cloud monitoring coverage
- Alignment with enterprise cybersecurity KPIs for risk and resilience
Reducing detection and response times often provides greater financial risk reduction than simply adding more security tools. Many enterprises at this stage evaluate centralized monitoring platforms or enterprise cybersecurity solutions that improve cross-environment visibility.
Enterprise Security Maturity Model
Enterprise Cybersecurity Strategy maturity generally evolves across progressive stages:
Level 1 – Reactive Security
- Tool-based protection
- Minimal executive reporting
- Incident-driven response
Level 2 – Structured Compliance
- Documented policies
- Framework alignment (ISO/NIST/SOC 2)
- Periodic audits
Level 3 – Integrated Governance and Enterprise Risk Management
- Risk quantified financially
- Executive dashboards
- Vendor risk integration
Level 4 – Proactive Resilience
- Continuous monitoring
- Zero Trust architecture
- Automated response workflows
Level 5 – Adaptive Security Leadership
- Predictive threat modeling
- Board-level cyber strategy
- Enterprise-wide security culture
Most mid-to-large enterprises operate between Levels 2 and 3. Strategic transformation occurs when organizations move from compliance-driven security to resilience-driven governance.
Industry benchmarking consistently shows that fewer than 20% of enterprises reach the highest levels of cybersecurity maturity, even with strong governance frameworks. Organizations that move beyond compliance toward resilience do so by aligning security initiatives with measurable executive KPIs and cross-functional governance mechanisms.
The Evolving Enterprise Threat Landscape
Understanding threat evolution is essential for strategic investment planning.
Ransomware and Double Extortion
Modern ransomware attacks are structured business models. Attackers often:
- Obtain initial access via phishing or stolen credentials
- Escalate privileges and map internal systems
- Exfiltrate sensitive data
- Encrypt systems and initiate double extortion
The financial impact extends beyond ransom demands. Downtime, regulatory reporting obligations, litigation exposure, and reputational damage often exceed the initial payment request.
For enterprises, resilience depends less on ransom negotiation and more on:
- Segmented architecture
- Offline backup validation
- Incident response readiness
- Rapid containment capability
Phishing and Credential Abuse
Phishing remains effective because it exploits behavioral patterns rather than technical flaws. AI-assisted message generation has increased the sophistication of impersonation attempts, including executive-style communication.
Effective mitigation combines:
- Multi-factor authentication (MFA)
- Behavioral anomaly detection
- Continuous employee awareness programs
- Rapid credential revocation workflows
Security awareness must evolve from annual compliance training to ongoing behavioral reinforcement.
Cloud Misconfiguration and Visibility Gaps
Cloud adoption increases agility but introduces configuration complexity. Over-permissioned identities, exposed storage buckets, and API-level weaknesses frequently result from fragmented governance rather than negligence, making cloud security compliance a critical requirement for enterprises.
Enterprises commonly strengthen posture through:
- Cloud security posture management (CSPM)
- Identity governance automation
- Continuous configuration auditing
- Centralized security dashboards
This stage often drives evaluation of scalable enterprise cloud security platforms that unify risk visibility across hybrid environments and provide consolidated compliance reporting.
Common Enterprise Security Failures
Even well-funded organizations frequently encounter recurring structural weaknesses:
- Overreliance on perimeter defenses
- Excessive privileged access accumulation
- Untested incident response plans
- Fragmented tool ecosystems with limited integration
- Security metrics disconnected from financial risk
These failures rarely stem from lack of investment. They typically result from misalignment between technical controls and governance strategy.
Enterprises that periodically reassess architecture, access governance, and monitoring integration significantly reduce these systemic weaknesses.
Security Frameworks and Governance Alignment
Frameworks such as ISO 27001 compliance guide, the NIST Cybersecurity Framework, and SOC 2 provide structured models for security governance and compliance alignment.
However, certification alone does not equal resilience.
Common gaps include:
- Policies documented but not operationalized
- Incident response plans that remain untested
- Limited executive-level reporting transparency
- Inconsistent vendor risk management
True enterprise maturity requires operational integration, measurable controls, and continuous improvement cycles within a clearly defined Enterprise Cybersecurity Strategy.
Executive Insight
Compliance demonstrates alignment.
Resilience demonstrates capability.
Organizations that treat frameworks as active governance systems—not static documentation—achieve both.
Zero Trust Architecture in Practice
Zero Trust architecture is an architectural philosophy built on continuous verification rather than implicit trust.
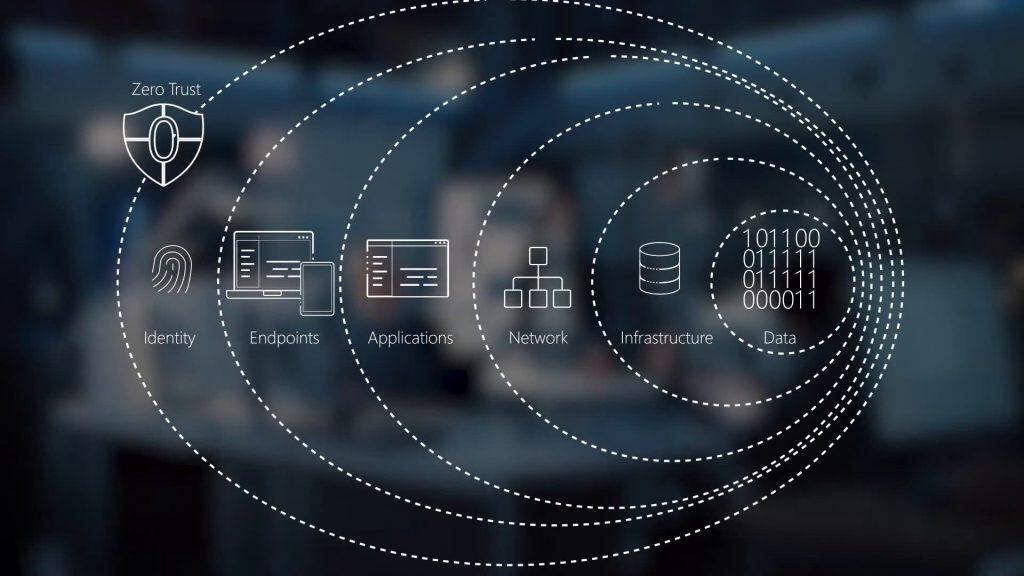
Traditional perimeter models assumed that users inside the network were safe. Enterprise cybersecurity strategy now assumes compromise is possible and designs controls accordingly.
Zero Trust Architecture principles typically include
- Continuous identity verification
- Device posture validation
- Least-privilege access enforcement
- Micro-segmentation of critical systems
- Real-time session monitoring
Implementation is phased and often begins with identity consolidation before extending to workload segmentation and application-layer controls.
When deployed effectively, Zero Trust reduces lateral movement risk and improves regulatory transparency.
Learn more about practical implementations in Zero Trust Security Model: How It Works for Enterprises.
Incident Response and Operational Resilience
Even mature enterprises must assume incidents will occur, which is why Enterprise Cybersecurity Strategy planning must prioritize structured incident response planning and operational readiness.
A structured incident response lifecycle includes:
- Detection and validation
- Immediate containment
- Investigation and forensic analysis
- Communication with stakeholders and regulators
- Recovery and restoration
- Post-incident review and control improvement
Organizations that conduct regular tabletop exercises demonstrate significantly improved containment performance and cross-functional collaboration.
At this maturity stage, many enterprises invest in advanced incident management platforms and integrated security operations capabilities to streamline response workflows and reduce mean time to containment.
How Enterprises Begin Strengthening Cybersecurity
Improving enterprise cybersecurity posture typically begins with foundational governance steps:
- Comprehensive cybersecurity risk assessment
- Asset inventory and dependency mapping
- Identity and access governance review
- Formal vulnerability management program
- Documented and tested incident response procedures
From there, organizations incrementally adopt advanced security architecture and scalable enterprise cybersecurity solutions aligned with business growth objectives.
Incremental, governance-aligned improvement is significantly more sustainable than reactive, tool-driven expansion.
Building a Security-Focused Enterprise Culture
Technology enables protection. Culture sustains it within a long-term Enterprise Cybersecurity Strategy.
Security-aware enterprises:
- Integrate cybersecurity reporting into executive dashboards
- Include vendor risk evaluation in procurement workflows
- Embed secure-by-design principles into product development
- Encourage transparent reporting of suspicious behavior
When cybersecurity is positioned as business enablement rather than operational friction, adoption and compliance improve organically.
Frequently Asked Questions About Enterprise Cybersecurity
What is enterprise cybersecurity?
Enterprise cybersecurity is a governance-driven strategy that protects organizational systems, data, and cloud environments through layered risk management, structured frameworks, identity controls, and continuous monitoring. It aligns security decisions with business objectives and regulatory compliance.
Why is cybersecurity critical for businesses today?
Cyber incidents can directly impact revenue, regulatory compliance, operational continuity, client trust, and even investor confidence. Effective enterprise cybersecurity mitigates these risks while enabling safe digital transformation and cloud adoption.
How do enterprises measure cybersecurity effectiveness?
Organizations use KPIs such as:
– Mean Time to Detect (MTTD)
– Mean Time to Respond (MTTR)
– Patch compliance rates
– Privileged access review frequency
– Coverage across critical IT systems
These metrics ensure that security is measurable, actionable, and aligned with business risk tolerance.
What is Zero Trust, and should my company implement it?
Zero Trust is an architectural philosophy based on continuous verification, least-privilege access, and device posture monitoring. While not mandatory, implementing Zero Trust significantly reduces lateral movement in breaches and supports regulatory transparency.
What common challenges do enterprises face with cybersecurity?
Common pitfalls include fragmented governance, untested incident response plans, insufficient executive oversight, over-reliance on tools instead of processes, and underestimating human factors like phishing. Addressing these challenges requires integration across IT, legal, finance, and operations.
Evaluating Enterprise Cybersecurity Solutions
When selecting enterprise cybersecurity platforms, organizations must prioritize risk visibility, integration capabilities, governance alignment, and scalability over isolated feature checklists. Modern enterprises lean toward solutions that centralize monitoring, unify third-party risk, and provide executive-ready dashboards with measurable KPIs such as MTTD (Mean Time to Detect) and MTTR (Mean Time to Respond).
Solutions that support continuous improvement cycles and align with frameworks like ISO 27001 and NIST CSF not only satisfy compliance but also enhance resilience and operational readiness.
Conclusion: Strengthening Enterprise Cybersecurity for Sustainable Growth
Enterprise Cybersecurity Strategy is no longer optional risk mitigation — it is strategic infrastructure that determines long-term organizational resilience, business resilience, and continuity. Organizations that embed structured frameworks, identity-centric controls, continuous monitoring, and a security-focused culture are better equipped to manage digital risk at scale.
By prioritizing measurable outcomes, executive engagement, and operational resilience, businesses can reduce financial and reputational impact, meet regulatory obligations, and confidently support growth and innovation.
Explore More on Enterprise Cybersecurity
- Best Cybersecurity Tools for Businesses
- Cybersecurity Compliance Explained: SOC2, ISO27001 & GDPR
- Zero Trust Security Model: How It Works for Enterprises
- Top Cybersecurity Threats Facing Businesses in 2026
- Cybersecurity Strategy for Small and Medium Businesses

